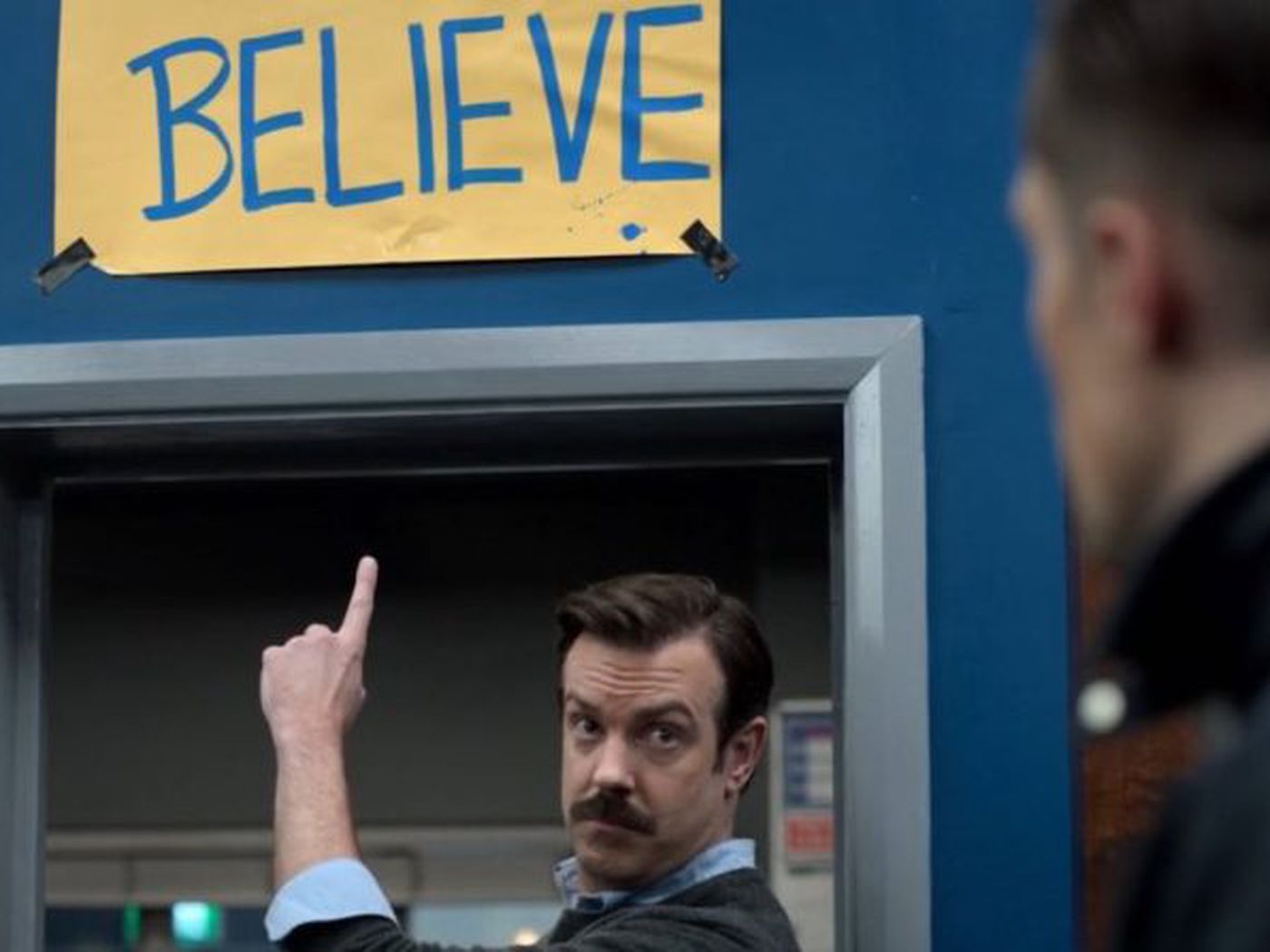
Ted Lasso’s Total Football and Cybersecurity Strategy
Over the past few weeks, I’ve been re-captivated by Total Football, primarily thanks to our favorite soccer coach, Ted Lasso. Watching Ted reimagine AFC Richmond’s strategy through a single epiphany, at a bar, while eating onion rings, is all too relatable for comfort. Luckily, this idea didn’t require me to consume more fried food than my body could handle; Ted did the heavy lifting for me. But after watching this scene, I realized, surprisingly, that the principles underlying Total Football bear a striking resemblance to building a robust cybersecurity strategy against social engineering attacks. Both realms require a dynamic mindset, fostering a culture of resilience and adaptability to counter ever-changing challenges. Before you call me crazy, let’s delve into this in more detail.
The Versatility of Players and Users
Total Football is a revolutionary football (soccer) tactic popularized by the 1970 Dutch national team, and perfected by Johan Cruyff during his time at Ajax and Barcelona FC. At the core of the strategy lies the idea that players should be versatile and adaptable, capable of seamlessly interchanging positions on the pitch. Similarly, in the realm of cybersecurity, organizations should cultivate a workforce that is versatile in their knowledge and preparedness against social engineering attacks. Rather than solely relying on security or IT professionals, all employees should have the skills and awareness to identify potential threats. By nurturing a cybersecurity mindset among all users, organizations can create a formidable proactive attack & defense similar to the high press of Total Football.
Fluid Communication and Collaboration
Total Football thrives on fluidity and teamwork, with players constantly aware of their teammates’ positions and movements. When a midfielder presses forward into the attack, a striker can fill in the space behind him/her to protect the space left open.
Likewise, in cybersecurity, effective communication and collaboration are paramount. Organizations should foster a culture where users feel comfortable reporting potential security incidents, sharing suspicious emails, or alerting their peers to possible social engineering attempts. By promoting open lines of communication and collaborative efforts, organizations can create a strong network of vigilant individuals who collectively safeguard against social engineering attacks.
At one of my previous companies, we had a dedicated Slack channel made for identifying potentially malicious phishing emails and text messages. Any employee was encouraged to post in the channel with no shame or repercussions. If anything, we would make fun of some of the hilarious phishing attempts such as this one:
Constant Adaptation and Training
In Total Football, players are not confined to rigid positions; they are encouraged to adapt and excel in different roles as the game demands. If the team is down by a goal, more defensive and midfield players will join the attack when the ball is won. Or the team will jointly press higher up the pitch to win the ball in the opposing team’s half. Forcing mistakes by the opposition and creating potential chances to score. Similarly, organizations must emphasize the importance of continuous training and adaptation to combat the evolving tactics employed by social engineering attackers. Regular cybersecurity awareness training sessions, simulated phishing campaigns, and knowledge-sharing initiatives help users stay informed and build their defense skills. This adaptive approach ensures that users remain prepared to detect and thwart the ever-changing methods used in social engineering attacks.
Proactive Detection and Response
Total Football teams employ proactive pressing and intense defensive pressure to regain possession quickly. The key here is proactively pressing, as many teams won’t press unless they’re a goal down or chasing the game. This is counter to Total Football as the team is encouraged to press at any point of the game.
Similarly, organizations must adopt an aggressive stance in detecting and responding to social engineering attacks. Implementing robust security controls, such as multi-factor authentication, email filtering systems, and endpoint protection, fortifies the organization’s defense. Additionally, establishing incident response protocols and conducting regular security assessments can help identify vulnerabilities and weaknesses before they can be exploited.
Taking the First Few Steps
By fostering versatility, fluid communication, continuous training, and proactive defense measures, organizations can build a resilient cybersecurity strategy that models Total Football. Although this strategy can be revolutionary, it can be daunting to take the first few steps. At Hada Security, we’re all about making your users an essential part of your cyber defense. We know that one solution doesn’t fit all. That’s why our set of security products and services meet our clients where they’re at in their security journey. Take the first steps with our 5-Minute Security Quiz – it’s a fun way to get started! Let us help make your business a fortress against cyber threats.